Newly identified cybergang uses vendor email compromise to spy on communications and steal millions out of the global supply chain, according to Agari.
Key Points Discovered:
- 500+ companies in 14 countries affected (97% of vendor victims in the US, Canada, and the UK)
- 700+ employee email accounts compromised with OneDrive and DocuSign credential phishing campaigns
- 20,000+ emails stolen since late-2018
- 39 employees compromised at a single US-based company
Agari, the next-generation Secure Email Cloud that restores trust to the inbox, has released a report, developed by the Agari Cyber Intelligence Division (ACID), that delves into the shadowy world of a West African cybercriminal organization ACID has dubbed Silent Starling.
Silent Starling’s preferred type of attack is a rapidly emerging form of business email compromise, one Agari has coined vendor email compromise (VEC). This type of attack is unique in that it targets the global supply chain, using incredibly realistic-looking emails to trick a supplier’s customers into paying fake invoices. Due to its covert nature, VEC is very difficult for legacy systems to detect.
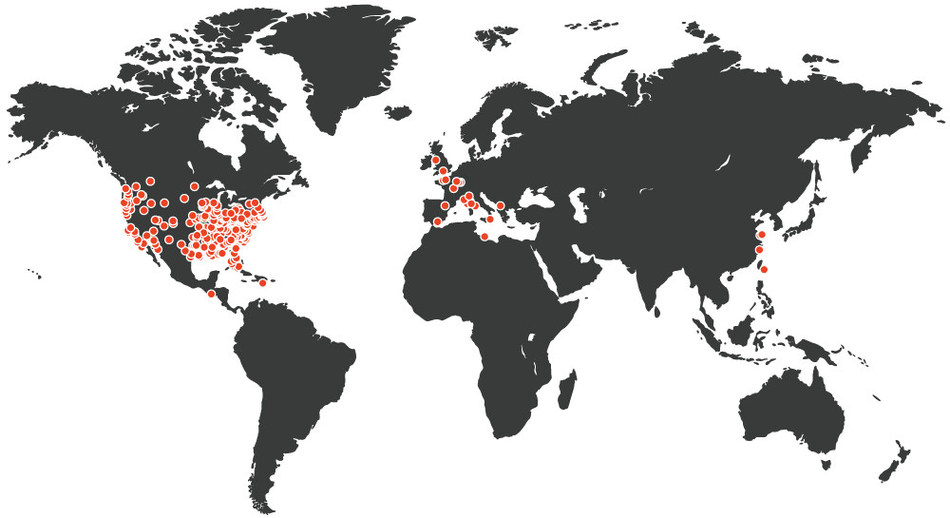
Cybergang Silent Starling targets victims in the U.S., Canada and the U.K.
To start their attack, Silent Starling associates hijack the email accounts of employees typically in a vendor’s finance department, like accounts receivable or procurement. They then patiently wait and spy on all communications coming into these compromised mailboxes, gathering intelligence, data and, critical context. This information enables Silent Starling associates to then craft and sends perfectly timed emails asking for an invoice to be paid, using the identity of the employee they have been spying on.
This type of attack is particularly hard to spot, as it mimics the look and feel of legitimate communication. The only difference is that the invoice sent to a vendor’s customer contains details for the scammer’s bank account instead of the vendor.
Legacy technology cannot pick up on socially engineered attacks backed by contextual information, making VEC the biggest threat coming around the corner.
“Our visibility into Silent Starling’s operations has given us a direct and in-depth look at how the entire VEC attack chain unfolds,” said Crane Hassold, senior director of threat research at Agari and head of ACID. “VEC is the next evolution of business email compromise (BEC). These attacks will continue to increase in frequency over the next 12 to 18 months because the financial return for scammers is very significant.”
Cumulative losses associated with this scam are difficult to calculate, as companies don’t reveal the information publicly unless included in an indictment. FinCEN recently reported that average VEC scam costs a victim company more than $125,000, compared to $50,000 in a classical CEO impersonation BEC attack.
Given the scale and severity of VEC, AI and machine learning technology is the only mechanism that stands a chance of mitigating attacks from Silent Starling and cybergangs like it.
Peterson concluded, “ACID is a tangible and outward sign of the fulfillment of Agari’s mission, which is to protect digital communications to ensure humanity prevails over evil.”
Register now for the Silent Starling webinar, hosted by Crane Hassold.

